Introducing val.run
Today we are introducing a new API scheme under the new val.run domain. In addition to an urgent security upgrade, the new API scheme is subdomain-based to leave the URL path clear for arbitrary webhook handlers. For example, this is what’s needed to create a ChatGPT plugin, Matrix Push Gateway, or Bluesky Feed Generator.
We had planned to roll this out more gradually over the coming months, but were recently alerted to a potential exploit with our Express API, so we rolled out this new API effective immediately. Going forward all requests to our v0 and v1 Express API redirect to val.run.
This will require no change if:
- You are using our Eval or Run APIs
- Your Express API usage is in a browser (which automatically follow redirects)
- You have
redirect: "follow"in your fetch requests to our Express API
If not, it is a simple URL scheme switch - our Upgrade Guide below will walk you through it. We attempted to contact our API users ahead of this change, but we apologize if you were caught unawares and this causes breaking changes for you. We take breaking changes seriously, and only choose this path reluctantly to protect against the new exploit that was reported. The vulnerability was not exploited to the best of our knowledge.
Overview
Val Town is a website for users to write and run JavaScript. User code can also be run via the API. The v0 API was launched in late 2022. The v1 API was launched on May 4th, 2023, along with Restricted Library Mode semantics. The v1 API has three modes, Express, Run, and Eval, which give various levels of convenience and customizability, depending on your needs.
Today’s new val.run API change only applies to our Express API. The exploit (explained below) relies running a client-side script on an HTML page, which is only possible in our Express API. The other two APIs (Eval and Run) only return JSON, thus are not affected, and are not being changed.
Upgrade Guide
The changes to the Express API:
- The domain is
express.val.runinstead ofapi.val.town - The username and val name are specified in the subdomain, not the URL path
- Requests old Express API are redirected to the new scheme, effective immediately.
These changes provide an isolated security model and allow for fully-customizable API paths, as required by some webhook specs.
| Before | Now |
|---|---|
| api.val.town/v1/express/user.val | user-val.express.val.run |
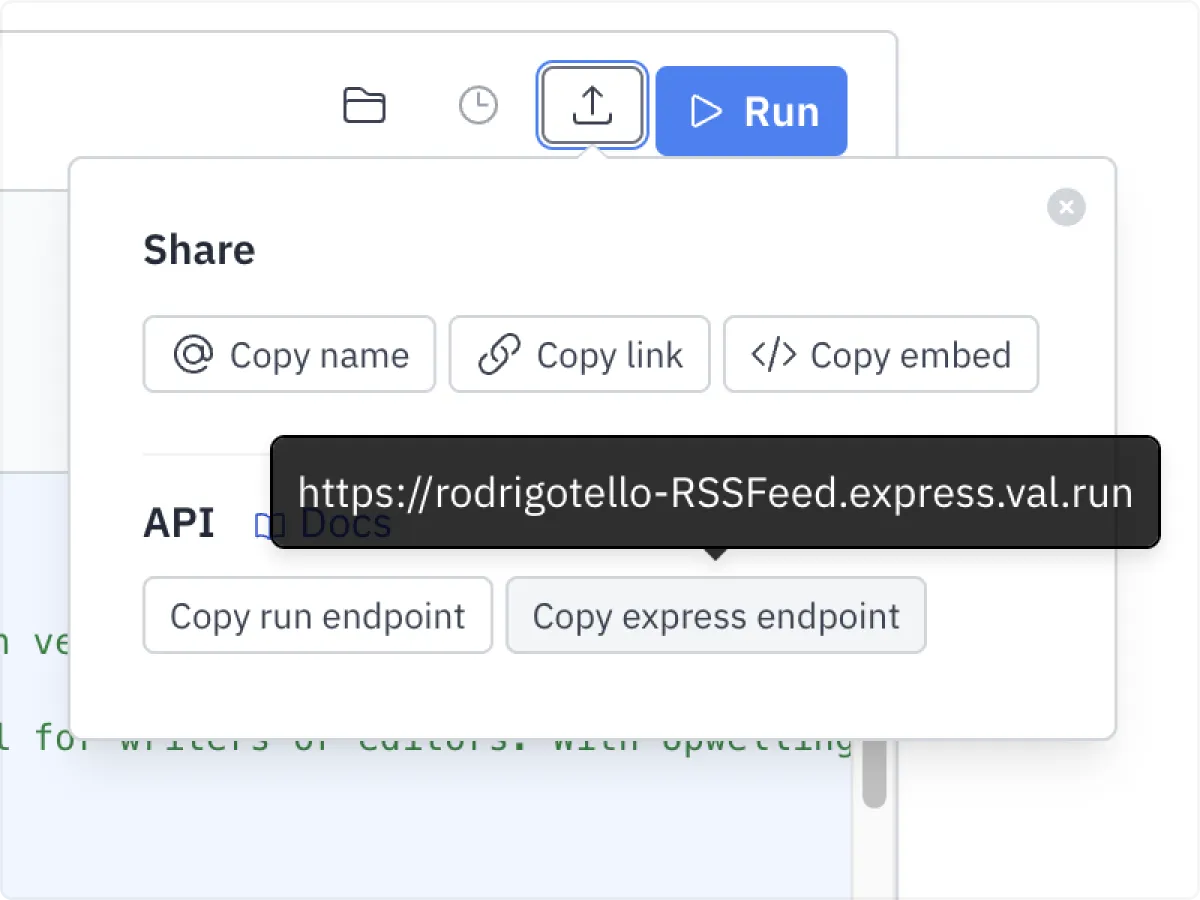
The share menus on vals now automatically point to the new Express API.
Exploit
The exploit was caused by how cookies are shared from parent domains to subdomains. It was responsibly reported by easrng.
- A malicious user makes an Express API val with the exploit (explained below)
- Another user that’s logged into val.town visits
api.val.town/v1/express/username.exploitVal - The exploit val returns a page with a client-side script
- The script authenticates to our authentication provider (Clerk)
- This succeeds because cookies from val.town are sent with requests made on api.val.town
- The user who made the exploit val now has the logged in user’s access token
- They could send it to themselves and gain full control over the Val Town account
This exploit was not taken advantage of to the best of our knowledge.
Contact
We at Val Town will be on call for the next couple days, so please reach out if you have any questions or concerns. Discord is great if it’s a public question and the community might be able to help. You can contact me personally at steve@val.town for anything at all.
Thanks for your help and patience through this change. We’re looking forward to seeing all your cool new GPT Plugins and other integrations this new API scheme enables!
Edit this page